Recently, NetDiligence (a company that provides cyber risk management and data breach services to cyber insurance professionals and their policyholders) issued its 15th annual Cyber Claims Study. This report is based on the statistical analysis of more than 10,000 cyber claims for insurance incidents that occurred between 2020 and 2024.
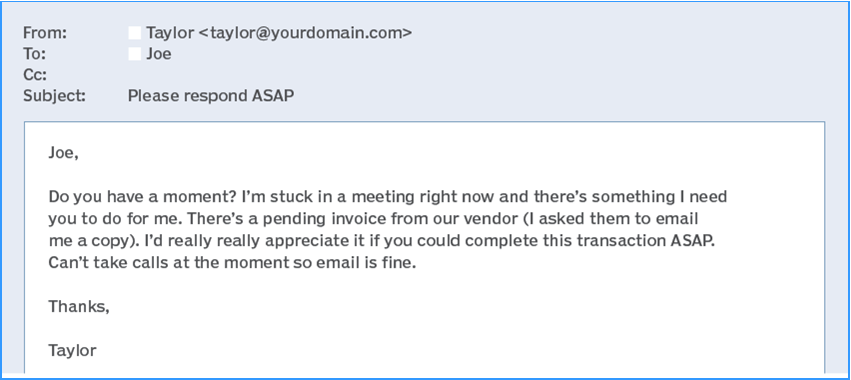
Among the key findings, ransomware and business email compromise were the two leading causes of loss. Specifically:
- 2,675 claims were due to ransomware, with 41% of these occurring between 2022 and 2024.
- 1,864 claims were because of business email compromise; 58% of which occurred between 2022 and 2024.
The overall average cost of an incident for small to medium-sized businesses was $264,000. That is a significant increase from last year’s $205,000. Similarly, the average payout rose from $167,000 to $183,000. The difference between the cost and the payout averaged $81,000 last year. That out-of-pocket expense means that some businesses were adversely affected by having to absorb that on their own.
The top four causes of loss were:
Ransomware
Business Email Compromise (BEC)
Hackers
Wire Transfer Fraud
The losses in these four categories accounted for 72% of claims and 85% of the total incident cost ($2 billion).
The number of ransomware incidents reported decreased from 757 in 2020 to 397 in 2024; however, the amounts and total incident cost have increased dramatically over the same time.
The five top affected business sectors included:
- Professional Services
- Manufacturing
- Healthcare
- Retail
- Financial Services
What amazes me is that last year, 4,000 new claims were submitted, bringing the total to 10,000. As a result, NetDiligence reports that total incident costs at SMBs are up in almost every category. The 30% increase in the five-year average cost came as a shock to the report writers.
And no insurance claims-related report can escape mentioning AI and its implications. Noted was the malicious use of AI, which has resulted in the explosive growth of criminal attacks on corporate networks. Credential phishing attacks increased by over 700% in the latter half of 2024, with more than 80% of phishing email messages utilizing AI technology. And yet, only a third of companies are using AI to fight fraud.
The report concludes that companies need to recognize that no defense is 100% secure and must increase their focus on being proactive and responsive. They urge companies to develop and regularly update an Incident Response Plan (IRP) to reflect current threats. The IRP should include specific playbooks for each of the four major types highlighted in this report, and it should be walked through so that everyone in the company who plays a role can respond effectively when (not if) a malicious incident occurs.
As is the case in almost every report, it ends by stating that cyber insurance should be a key consideration, but only as a safety net, not as a substitute for good security practices.
Thanks, and safe computing!